
The Fourth Industrial Revolution is not about buying new technology; it is a fundamental strategic shift toward a new operating model based on systems thinking.
- Success hinges on orchestrating interconnected cyber-physical systems, not simply upgrading isolated machinery or software.
- True ROI comes from mastering the operational logic of this new model, focusing on incremental digitization and workforce empowerment.
Recommendation: Begin by evaluating your current operations through the lens of cyber-physical integration and focus on a phased modernization strategy that prioritizes operational continuity and upskilling your existing teams for digital monitoring roles.
For any non-tech executive, the constant barrage of terms like “AI,” “IoT,” “blockchain,” and “digital twin” can feel overwhelming. There’s an immense pressure to “digitally transform” or risk being left behind, a pressure often amplified by consultants who speak in code and promise silver-bullet technology solutions. The common advice is to invest heavily in data infrastructure and embrace agile methodologies, but this often misses the fundamental point for leaders in manufacturing, logistics, and other traditional sectors.
The conversation is too often about the technology itself, rather than the new business physics it enables. What if the goal isn’t to become a tech company, but to become a traditional company that thinks and operates with the efficiency of one? The real revolution isn’t in the isolated adoption of new tools. It’s in the strategic shift from managing physical assets to orchestrating cyber-physical systems—integrated networks where software and hardware are in constant dialogue to optimize real-world outcomes.
This isn’t about you becoming a coder or a data scientist. It’s about you, as a leader, understanding this new operational paradigm to ask the right questions, make smarter investment decisions, and guide your organization through a pragmatic, ROI-driven evolution. This guide offers a playbook to do just that, moving beyond the buzzwords to focus on tangible strategies for modernizing legacy systems, securing your smart factory, and empowering your workforce for the future.
To navigate this complex landscape, it’s essential to break down the core challenges and opportunities. This article provides a structured path, from understanding the foundational concepts to implementing practical, high-impact strategies on your factory floor and across your supply chain.
Summary: A Non-Tech Leader’s Guide to Industry 4.0 Strategy
- Why Cyber-Physical Systems Are the Backbone of Future Production?
- How to Digitize a 30-Year-Old Supply Chain Without Halting Operations?
- Retrofitting or Replacing: Which Strategy Offers Better ROI for Machinery?
- The Cybersecurity Oversight That Exposes Smart Factories to Ransomware
- How to Upskill Manual Operators for Digital Monitoring Roles Effectively?
- Why Immutable Ledgers Prevent Counterfeit Goods in Luxury Markets?
- How to Bypass Ad Blockers Legally with Server-Side Tracking?
- How Smart Factories Use Machine Learning to Predict Maintenance Needs?
Why Cyber-Physical Systems Are the Backbone of Future Production?
Forget thinking about software and machinery as separate entities. The core of the Fourth Industrial Revolution is the fusion of the physical and digital worlds into a single, intelligent entity: the cyber-physical system (CPS). Imagine your factory not as a collection of machines, but as a living organism where sensors (the nerves) feed real-time data to a central software brain (the mind), which then directs the machinery (the body) to act. This is the essence of CPS, and it’s the true engine of future production.
This shift is already underway and accelerating. A recent Gartner forecast predicts that by 2027, 80% of manufacturing operations management solutions will be cloud-native and edge-driven. This indicates a massive migration from siloed, on-premise control systems to interconnected, intelligent networks. This network allows for the creation of a “digital twin”—a live virtual model of your entire operation—that you can use to simulate changes, predict failures, and optimize performance without risking physical downtime.
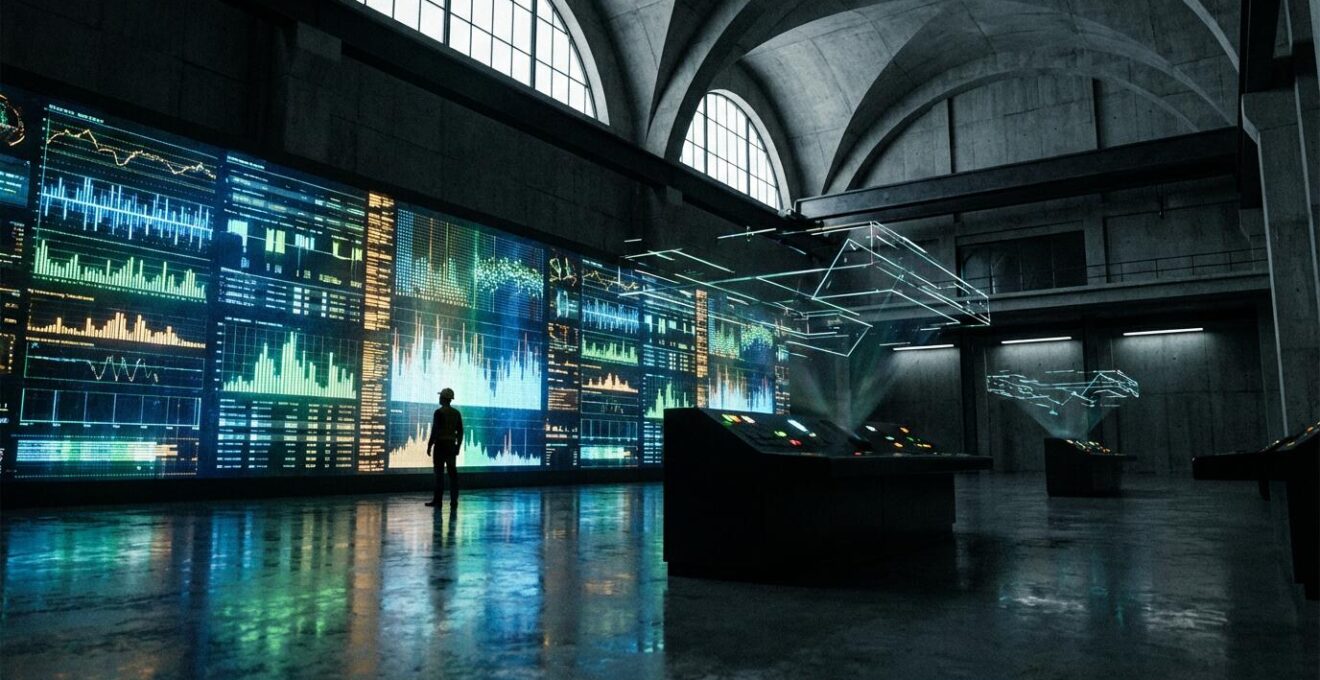
As the image of a control room monitoring a digital twin suggests, the focus moves from supervising individual machines to orchestrating the entire system. This enables new business models focused on outcomes, not just products. For instance, consider how Google’s DeepMind AI uses cyber-physical principles in healthcare. The system analyzes eye scans to detect diseases, offering “diagnosis-as-a-service.” The value isn’t the scanner (the physical asset) but the accurate, life-saving insight (the cyber-physical outcome). For a non-tech executive, grasping this concept is crucial: your future value lies not just in what you make, but in the intelligent services your integrated systems can provide.
How to Digitize a 30-Year-Old Supply Chain Without Halting Operations?
The thought of overhauling a legacy supply chain—the operational heart of your business for decades—is daunting. The risk of disruption, downtime, and massive capital expenditure can lead to strategic paralysis. However, the solution isn’t a “rip and replace” approach. The most pragmatic and effective strategy for this “legacy-to-live transition” is an incremental methodology known as the Strangler Fig Pattern. Named after a vine that slowly envelops and replaces its host tree, this pattern allows you to modernize your system piece by piece while the old system continues to run.
The process is methodical and risk-averse. Instead of a single, high-stakes launch, you build new, cloud-native services around the edges of your legacy system. An API layer acts as a universal translator, allowing the old and new components to communicate seamlessly. As each new microservice is tested and proven stable, it takes over a function from the old system, which is then gradually “strangled” and decommissioned. This approach ensures zero-downtime operations and allows you to fund the transformation through the very efficiencies the new components generate.
This gradual investment is becoming the norm, as a 2024 Gartner survey found that 54% of manufacturing businesses plan to increase their software spending by 10% or more. This signals a clear move toward continuous, manageable upgrades rather than massive, one-off overhauls. The Strangler Fig Pattern provides a clear, actionable roadmap for this journey:
- Map Dependencies: Identify the lowest-risk components of your legacy system to target for the initial migration.
- Create an API Gateway: Build a universal communication layer that allows new and old systems to exchange data without forcing immediate replacement.
- Replace Incrementally: Develop and deploy new microservices one by one, thoroughly testing each before decommissioning its legacy equivalent.
- Monitor Performance: Use real-time metrics to compare the new components against the old, validating efficiency gains and ROI at each step.
- Expand Gradually: As confidence grows and value is demonstrated, systematically expand the scope of replacement, maintaining operational stability throughout the process.
Retrofitting or Replacing: Which Strategy Offers Better ROI for Machinery?
Once you’ve committed to building a cyber-physical operation, a critical investment question arises: should you retrofit your existing machinery with sensors and IoT gateways, or undertake the massive capital expenditure of a full replacement? There is no one-size-fits-all answer. The decision is a complex trade-off between initial cost, long-term capability, and strategic flexibility. For a non-tech leader, this decision must be driven by a clear-eyed analysis of operational ROI, not just technological novelty.
Retrofitting is often the path of least resistance. It involves adding a “digital layer” to your existing analog equipment, which is significantly cheaper and faster to implement. This approach can get you 80% of the way there, providing valuable data on machine uptime, output, and energy consumption. However, it has its limits. The data you can collect is constrained by the add-on sensors, and your future flexibility is tethered to the underlying legacy architecture. It’s a powerful first step, but it may not be the final one.
Full replacement, while prohibitively expensive upfront, offers a clean slate. New machinery comes with native analytics capabilities, generating a full spectrum of data that can be used for advanced applications like predictive maintenance and quality control. Critically, it also offers complete optionality for future products and processes that haven’t even been conceived yet. This table provides a clear framework for weighing the key factors:
| Factor | Retrofitting | Full Replacement |
|---|---|---|
| Initial Investment | 30-50% of new equipment cost | 100% capital expenditure |
| Implementation Time | 2-6 months | 6-18 months |
| Data Generation Capability | Limited to add-on sensors | Native full-spectrum analytics |
| Future Flexibility | Constrained by legacy architecture | Full optionality for unknown products |
| Talent Attraction Impact | Minimal – perceived as outdated | Significant – modern tech attracts engineers |
Ultimately, the right choice depends on your strategic horizon. If you need immediate data and are operating in a stable market, retrofitting delivers fast, tangible ROI. But if you are positioning your company for long-term disruptive growth, the investment in new equipment can be a powerful competitive moat. As research from the McKinsey Global Institute highlights, this decision has profound financial consequences: companies with strong digital and AI skills earn two to six times higher shareholder returns than their peers in every sector studied.
The Cybersecurity Oversight That Exposes Smart Factories to Ransomware
As your factory becomes “smarter” by connecting operational technology (OT)—the machines, controllers, and sensors on the factory floor—to your corporate IT network, you inadvertently open a new, highly vulnerable front in the cybersecurity war. The most dangerous oversight a non-tech executive can make is assuming that standard IT security measures are sufficient to protect the factory floor. They are not. OT systems speak a different language, have different vulnerabilities, and a breach has far more devastating consequences, potentially causing physical damage or a complete production shutdown.
Hackers know this. They see industrial control systems as high-value targets for ransomware because the cost of downtime is astronomical, making companies more likely to pay. The core issue is the fragile digital-physical interface. An attack that might just steal data from an IT server can be used to manipulate a robotic arm or shut down a cooling system in an OT environment. The industry’s adaptation is dangerously slow; Gartner highlights this critical security gap, noting that by 2026, a mere 15% of supply chain software offerings will use software bills of materials (SBOMs) to help counter cyberattacks.

Protecting a smart factory requires a dedicated OT/IT convergence security framework. This starts with visibility—you cannot protect what you cannot see. It requires segmenting your networks to create “air gaps” that prevent an infection in your email system from spreading to your production line. Most importantly, it requires specialized monitoring tools designed to understand industrial protocols and an incident response playbook tailored to factory-floor scenarios, including manual override procedures for critical machinery.
Your 5-Point OT Security Audit Plan: Securing the Digital-Physical Interface
- Points of contact: Identify and list all network channels and physical ports where operational technology (OT) connects with the corporate IT infrastructure.
- Collecte: Create a comprehensive inventory of all connected OT devices, including PLCs, sensors, and industrial robots, noting their software versions and patch status.
- Cohérence: Confront the current security protocols with OT-specific standards (like ISA/IEC 62443), identifying gaps between IT-centric policies and factory-floor needs.
- Mémorabilité/émotion: Analyze incident response plans to spot unique OT failure scenarios (e.g., physical equipment malfunction) versus generic IT threats (e.g., phishing).
- Plan d’intégration: Develop a prioritized roadmap to implement network segmentation, deploy specialized OT monitoring tools, and phase out insecure legacy devices.
How to Upskill Manual Operators for Digital Monitoring Roles Effectively?
The greatest asset in your 30-year-old factory isn’t the machinery; it’s the people who have run it for decades. They possess an invaluable, intuitive understanding of the production process. As you digitize, the biggest mistake is to see these experienced operators as obsolete. The real opportunity is to upskill them, transforming their deep domain knowledge into a powerful asset for the digital age. Yet, this is a major challenge; research reveals that 63% of executives believe their workforce is unprepared for the coming technology changes.
The goal is not to turn a machine operator into a software developer. It’s to empower them to become a data-informed decision-maker. Instead of just listening to a machine for signs of trouble, they will be trained to monitor a dashboard that visualizes data from a dozen machines simultaneously. Their role shifts from reactive manual labor to proactive digital supervision. They use their years of experience to interpret the data, spot anomalies the software might miss, and provide crucial context that no algorithm can replicate.
This transformation is not theoretical; it’s a proven strategy for success. Consider the World Economic Forum’s project to introduce technology to small and medium-sized farms in Colombia. This initiative equipped traditional farmers with soil sensors, climate data, and AI-powered insights. They were not replaced by technology; they were empowered by it. The results were staggering: farmers reduced their costs by 30% and increased their yields by 20%. This case study perfectly demonstrates that the most effective digital transformation is one that augments human expertise, rather than attempting to replace it. An effective upskilling program focuses on data literacy, dashboard interpretation, and collaborative problem-solving between operators and data analysts.
Why Immutable Ledgers Prevent Counterfeit Goods in Luxury Markets?
For industries where brand integrity and product authenticity are paramount, such as luxury goods, pharmaceuticals, or high-end electronics, the threat of counterfeiting is an existential one. The Fourth Industrial Revolution offers a powerful antidote: immutable ledgers, most commonly known as blockchain. At its core, a blockchain is simply a digital record of transactions that is permanent and tamper-proof. For a non-tech leader, you can think of it as a universal, unforgeable digital certificate of authenticity that travels with a product from its creation to the end customer.
The process creates an unbroken chain of provenance. When a luxury handbag or a precision watch is manufactured, it is assigned a unique digital identity (often a non-fungible token, or NFT) that is recorded on the blockchain. Every time that product moves through the supply chain—from the factory to the distributor, to the retailer—a new transaction is added to its digital ledger. This creates a permanent, verifiable history that anyone can access.
This has two transformative benefits. First, it empowers the end customer. By scanning a QR code or an embedded NFC chip on the product with their smartphone, they can instantly view its entire history and confirm its authenticity, completely eliminating the guesswork of identifying fakes. Second, it creates a secure foundation for the secondary market. Brands can establish certified resale marketplaces where ownership of the physical item is transferred alongside its digital twin, ensuring legitimacy and capturing value from second-hand sales. For a CEO, this technology is not a complex cryptographic puzzle; it is a powerful tool for brand protection, customer trust, and market control. Implementing such a system involves a few key steps:
- Create a unique “digital twin” NFT for each physical product at the point of manufacture.
- Record all supply chain touchpoints on the immutable ledger, creating a permanent provenance trail.
- Enable customer verification through a smartphone app that scans an embedded chip or QR code.
- Establish a certified resale marketplace that leverages blockchain authentication for transfers of ownership.
- Analyze aggregated, anonymized transaction data to identify market trends and potential counterfeit hotspots.
How to Bypass Ad Blockers Legally with Server-Side Tracking?
While much of the Fourth Industrial Revolution focuses on the factory floor, the principle of “systems thinking” applies equally to customer-facing functions like marketing. A common pain point for any modern business is data loss from ad blockers and browser privacy restrictions. Traditional client-side tracking, which relies on code running in the user’s browser, is increasingly unreliable. Server-side tracking offers a more robust and compliant solution by shifting the data collection process from the user’s device to your own controlled server environment.
This isn’t about “spying” on users; it’s about reclaiming ownership of your first-party data and ensuring its accuracy. With client-side tracking, when a user visits your website, tracking scripts from Google Analytics, Facebook, and others are loaded directly in their browser. These are easily identified and blocked. With server-side tracking, only a single, first-party data stream is sent from the user’s browser to your server. From there, your server decides which information to securely and anonymously forward to your marketing partners. Because the communication happens server-to-server, it is invisible to ad blockers.
This approach offers superior data accuracy and faster page load times, improving the user experience. However, it requires a higher level of technical implementation and a commitment to transparency. You must still disclose your data practices in your privacy policy. The strategic choice between these two methods comes down to control versus convenience, as this comparison shows:
| Aspect | Client-Side Tracking | Server-Side Tracking |
|---|---|---|
| Ad Blocker Vulnerability | Blocked by 30-50% of users | Undetectable by blockers |
| Data Accuracy | Subject to browser limitations | Near 100% accuracy |
| Implementation Complexity | Simple JavaScript tags | Requires server infrastructure |
| Privacy Compliance | Visible to users | Requires transparent disclosure |
| Page Load Impact | Slows by 15-30% | No client performance impact |
For a non-tech leader, the key takeaway is strategic: relying solely on third-party, client-side tracking means you are building your data strategy on rented land. Investing in a server-side infrastructure is a move toward data sovereignty, giving you a more accurate and resilient foundation for understanding customer behavior in a privacy-first world.
Key Takeaways
- Shift Your Mindset: The Fourth Industrial Revolution is a strategic challenge of orchestrating cyber-physical systems, not just a technological one.
- Prioritize Pragmatic Modernization: Use incremental strategies like the “Strangler Fig Pattern” and make smart ROI-based decisions between retrofitting and replacing machinery.
- Invest in Humans and Security: Your greatest assets are your experienced operators and the security of your production line. Focus on upskilling and implementing a dedicated OT security framework.
How Smart Factories Use Machine Learning to Predict Maintenance Needs?
Predictive maintenance is perhaps the most powerful and tangible application of cyber-physical systems in a modern factory. It represents the ultimate shift from a reactive to a proactive operational model. For decades, maintenance has followed two logics: run-to-failure (fix it when it breaks) or preventative (fix it on a schedule, whether it needs it or not). Both are inefficient. Predictive maintenance introduces a third, far more intelligent option: fix it just before it breaks.
This is made possible by machine learning algorithms that analyze data from sensors on your equipment. These sensors monitor vibrations, temperature, acoustics, and other performance indicators. The algorithm learns the “normal” operating signature of a healthy machine. When it detects subtle deviations from that signature that signal an impending failure—long before a human could notice—it automatically triggers a maintenance alert. This allows you to schedule repairs during planned downtime, order parts in advance, and avoid catastrophic, production-halting failures. This is not a futuristic vision; it’s a practical tool for maximizing operational ROI.

This data-driven approach is becoming the new standard as the workforce itself transforms. As Gartner forecasts, by 2028, there will be more smart robots than frontline workers in key sectors, driven by labor shortages. In this environment, maximizing the uptime and efficiency of every automated asset through predictive intelligence is no longer a luxury but a necessity for survival. The value is immense, reducing maintenance costs, extending equipment lifespan, and dramatically improving overall equipment effectiveness (OEE). As Paul Gaffney, a technology and supply chain leader, noted, this revolution is different because it’s “probably creating more brand new things than anything before it.”
Unlike all three prior revolutions, it’s probably creating more brand new things than anything before it.
– Paul Gaffney, Chief Technology and Supply Chain Officer at Kohl’s
The journey into the Fourth Industrial Revolution is not a technical sprint but a strategic marathon. It demands a new way of thinking, where leaders orchestrate systems rather than just manage assets. Begin today by evaluating your operations through the lens of cyber-physical integration, empowering your people with data, and implementing a pragmatic, ROI-focused roadmap to build a resilient, future-proof enterprise.